Home / PC Care Tool / Keylogger
Keylogger

Keylogger is easy to use surveillance tool featuring with extremely easy to use interface that makes an ideal choice for home and office users. PC monitoring tool automatically records all typed keystrokes including (typed email, chats records, website URL visited, password and other documents) in encrypted log files with option to send the activity log at specified email address. Invisible keylogger is solution for parents who want to monitor their child activities performed on the computer in their absence and similarly helps the corporate sector to keep track over their employee’s daily activities.
Stealth keylogger is comprehensive tool for monitoring your computer providing with features and runs invisibly underneath the operating system without getting noticed by anyone excepting the system owner. Allows you to secretly track and record all user’s activities on any PC or Laptop without being physically present in front of monitored computer.
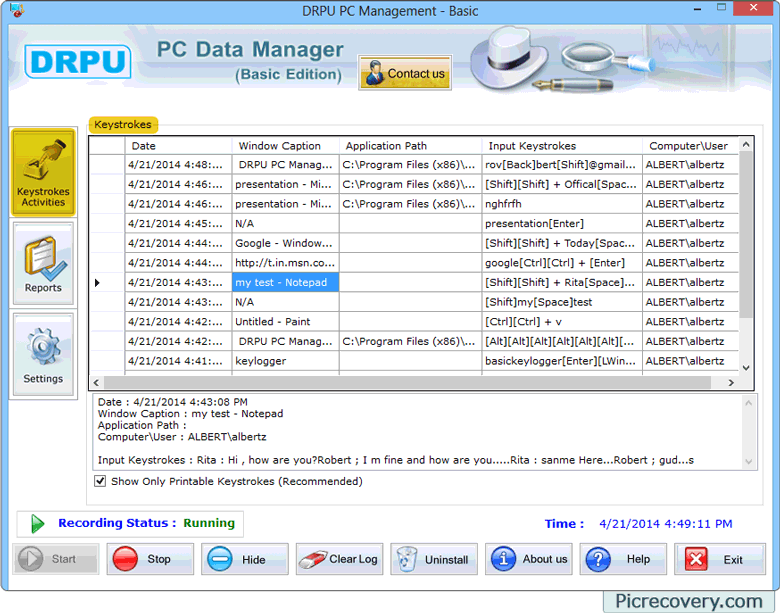
Screenshot of Keylogger
Monitoring Features
- 👉Records every keystroke typed by user on your computer machine in your absence.
- 👉Monitors and records each typed website url, visited web pages along with name and website title.
- 👉Logs all chat conversations made by user on Yahoo, Gmail, MSN and more.
- 👉Records emails sent by user from monitored PC.
Other Features
- 👉Recorded activity files can be delivered to specified e-mail address at set intervals to check the logs from distant location.
- 👉Reports of recorded logs can be easily generated in txt or html format as per user choice.
- 👉Runs silently in your PC and remains hidden in Desktop items, Program Files, Startup menu and installation folder path.
- 👉Allows users to set Hot keys or Run command to access program window while running in hidden mode.
- 👉Keystroke recorder software is safe and easy to use.
- 👉Software can be easily configured to start monitoring PC on windows startup.
- 👉Password protected features will never allow unauthorized user to access logs files and software settings.


